SonarQube in DevSecOps: Ensuring Code Quality and Security in the SDLC

🚀 Passionate DevOps Engineer | Python Developer | Startup Specialist Welcome to my LinkedIn profile! I'm Shaik Khadar Basha, a driven DevOps engineer with expertise in Kubernetes, Terraform, Python, and CI/CD. With a career rooted in startups like Netskope, Nyletech, and my current role, I excel in building scalable solutions, optimizing workflows, and thriving in high-growth, fast-paced environments. 🔧 Technical Expertise DevOps Tools: Kubernetes, Terraform, Docker, Jenkins, GitLab CI/CD Cloud Platforms: AWS, Azure, GCP Monitoring & Logging: Prometheus, Grafana, Splunk Languages: Python, Groovy, YAML Security: DevSecOps integration with tools like SonarQube, Aqua Trivy, SAST, and DAST 🚀 Key Achievements Startup Success: Played a pivotal role in scaling DevOps processes and implementing CI/CD pipelines, enabling rapid delivery cycles and growth in startup environments. Cost Optimization: Reduced cloud infrastructure costs by 20% while enhancing system performance by 15% through Terraform automation. Process Efficiency: Boosted delivery speed and deployment efficiency by 15% with robust CI/CD pipelines. Hackathon Recognition: Finalist in the Netskope Hackathon, showcasing a groundbreaking cloud security policy recommendation system. Team Leadership: Built high-performing DevOps teams, fostering a culture of collaboration and innovation in high-pressure startup settings. 🌟 Thriving in Startups Working in startups has shaped my ability to adapt quickly, innovate under constraints, and deliver impactful results. I take pride in wearing multiple hats, streamlining processes, and driving efficiency to support rapid scaling and business goals. 🌐 Areas of Expertise CI/CD Pipelines: Designing and implementing pipelines for faster, reliable releases Automation: Simplifying infrastructure and deployment processes Python Development: Building scalable, production-ready applications Cross-functional Collaboration: Ensuring seamless communication and delivery 🤝 Let’s Connect I’m eager to network with professionals who share my passion for DevOps, startups, and innovative technology trends. Let’s collaborate, share insights, or explore opportunities: shaik.badsha@gmail.com Thank you for visiting my profile—let’s build the future together!
Introduction
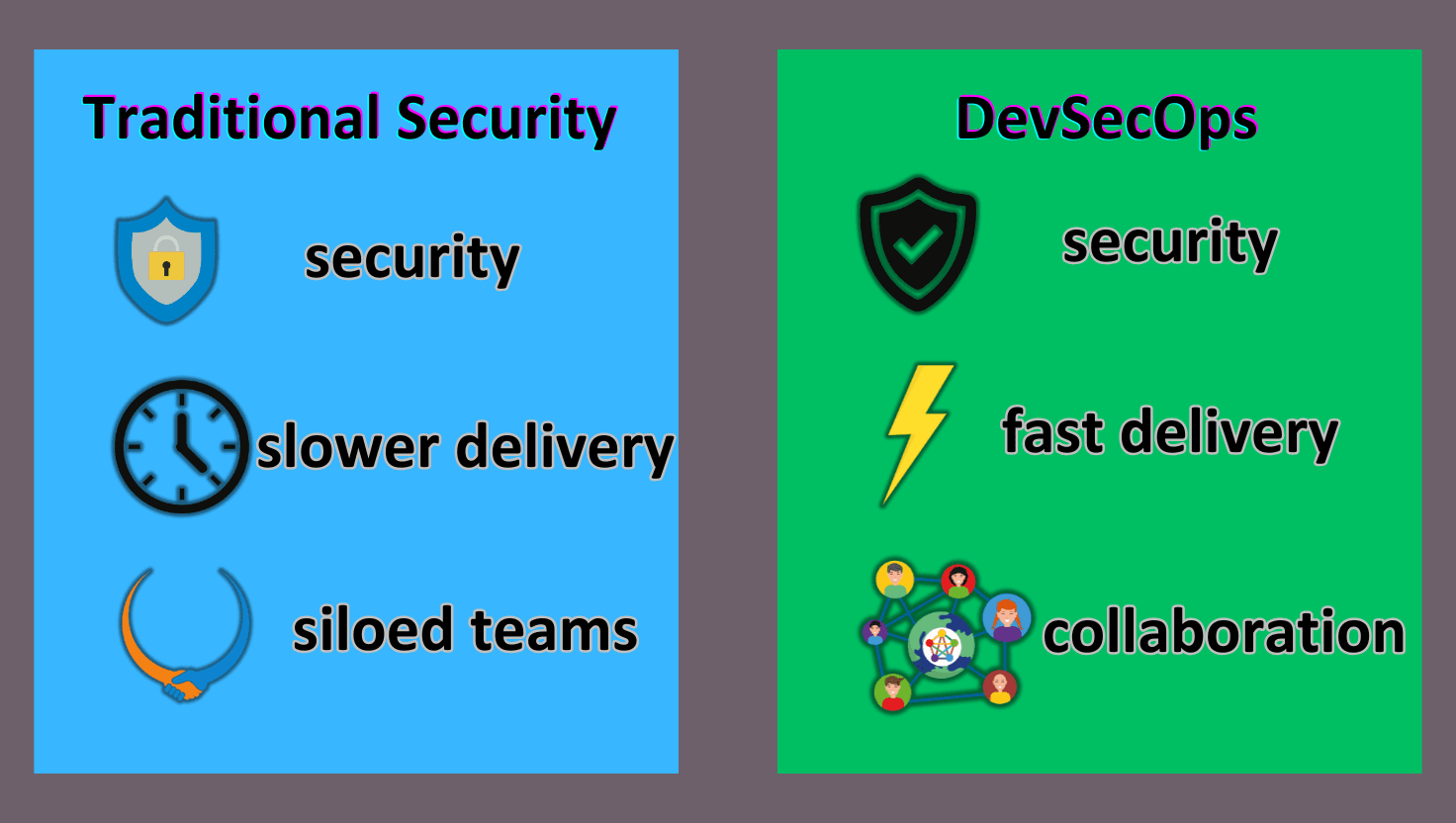
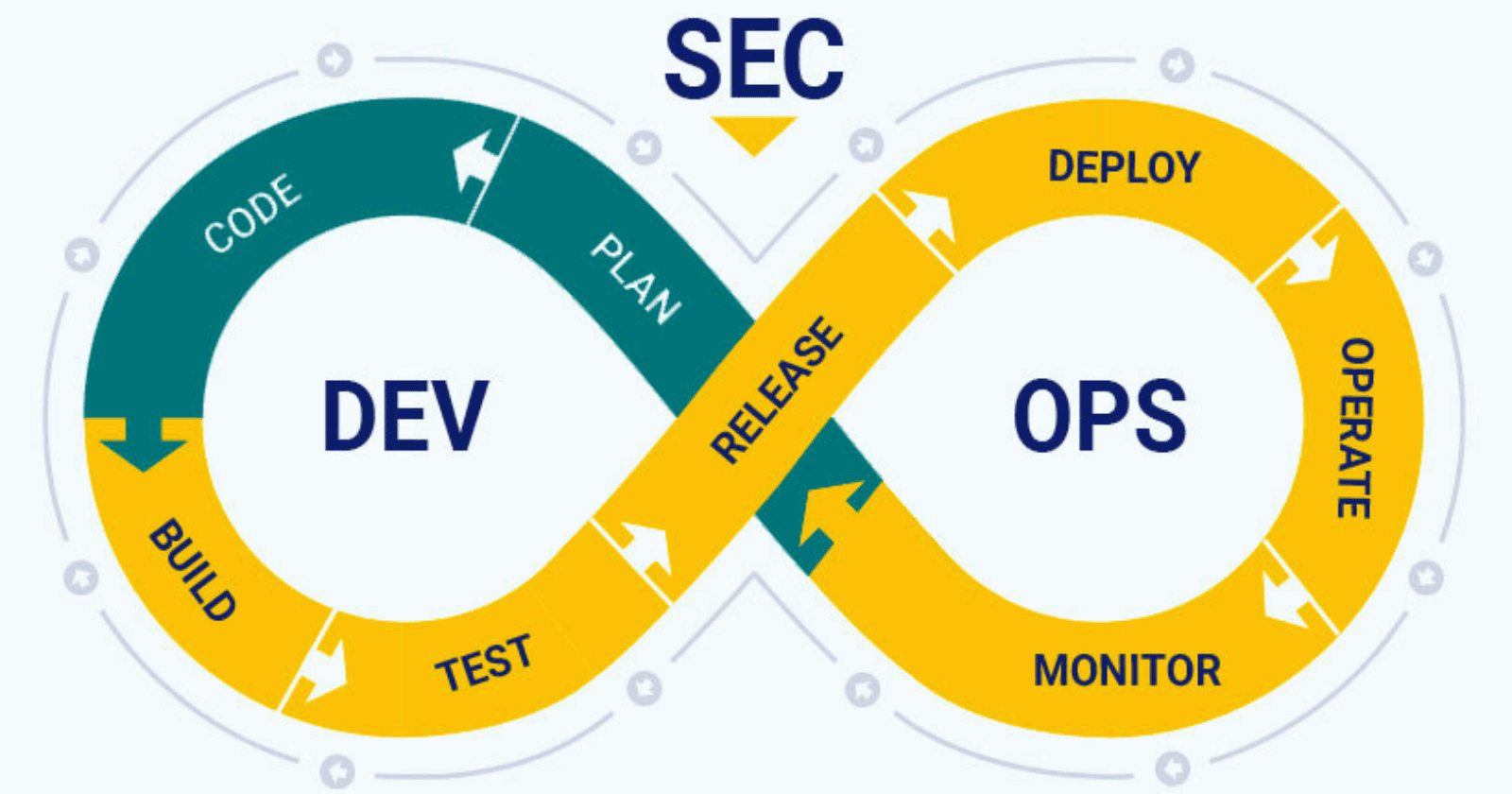
In today’s fast-paced software development world, security can no longer be an afterthought. DevSecOps—the integration of security into DevOps practices—has become a cornerstone of modern software development lifecycles (SDLCs). One critical tool for implementing DevSecOps effectively is SonarQube, an open-source platform designed to ensure code quality and identify vulnerabilities early in the development process.
This blog explores how SonarQube fits into the DevSecOps paradigm, its benefits, and practical ways to integrate it into your workflows.
What is SonarQube?
SonarQube is a powerful code quality and security analysis tool that helps developers identify bugs, vulnerabilities, and code smells in their projects. It supports over 30 programming languages and provides actionable insights to improve code maintainability and security.
Key features of SonarQube include:
Static Code Analysis: Automatically scans your codebase to detect issues without executing the code.
Security Hotspots and Vulnerabilities: Flags code segments that may be susceptible to security breaches.
Code Quality Metrics: Tracks technical debt, code duplication, and complexity.
CI/CD Integration: Seamlessly integrates into popular CI/CD pipelines like Jenkins, GitLab CI, and GitHub Actions.
Why SonarQube in DevSecOps?
The relevance of SonarQube in a DevSecOps setup stems from its ability to bridge the gap between developers, security teams, and operations. Here’s why SonarQube is essential in DevSecOps:
Shift-Left Security: By integrating SonarQube early in the SDLC, you can catch security vulnerabilities and coding issues before they progress downstream, reducing the cost of remediation.
Continuous Security Validation: SonarQube provides ongoing monitoring of code changes, ensuring new vulnerabilities or bad practices don’t creep into your applications.
Compliance: It supports compliance with standards like OWASP Top 10, SANS Top 25, and industry regulations, making it easier to meet security requirements.
Automation in CI/CD Pipelines: With SonarQube integrated into CI/CD pipelines, builds can fail automatically if the code quality or security thresholds aren’t met, ensuring quality gates are adhered to.
Practical Steps to Integrate SonarQube in DevSecOps
To effectively use SonarQube in a DevSecOps environment, follow these actionable steps:
1. Set Up SonarQube
Deployment: Install SonarQube on-premises or use its cloud version based on your organization’s needs.
Plugins: Install plugins for additional language support or specific rulesets, such as OWASP dependency checks.
2. Integrate with Source Control Management (SCM)
Link SonarQube with your version control systems like GitHub, GitLab, or Bitbucket to analyze pull requests and commits.
Use branch analysis to ensure every code branch maintains quality standards.
3. Incorporate into CI/CD Pipelines
Configure SonarQube scans as a step in your CI/CD pipelines using tools like Jenkins, Azure DevOps, or GitHub Actions.
Set up quality gates to fail builds when thresholds for bugs, vulnerabilities, or code coverage aren’t met.
4. Customize Quality Profiles and Gates
Tailor rulesets for your project based on the languages and frameworks you’re using.
Define quality gates that align with your organization’s risk tolerance.
5. Enable Developer Feedback Loops
Use SonarLint, an IDE extension, to give developers real-time feedback on code quality as they write it.
Encourage developers to address issues locally before pushing changes.
6. Monitor and Report
Leverage dashboards to track key metrics like code coverage, vulnerabilities, and technical debt.
Share periodic reports with stakeholders to maintain transparency and alignment.
Real-World Example: SonarQube in Action
A fintech company faced challenges maintaining security compliance while scaling its microservices architecture. By integrating SonarQube into their GitLab CI pipeline, they achieved the following:
Reduced critical vulnerabilities by 85% in three months.
Automated quality checks, resulting in faster feedback cycles for developers.
Improved code maintainability, reducing technical debt by 30%.
This implementation not only enhanced security but also boosted developer productivity and confidence in their code.
Tips for Maximizing SonarQube’s Potential
Train Teams: Ensure developers and DevSecOps teams understand how to interpret and act on SonarQube reports.
Regular Updates: Keep SonarQube and its plugins updated to leverage the latest features and vulnerability databases.
Start Small: Begin with non-blocking quality gates and gradually tighten thresholds as the team matures.
Combine Tools: Use SonarQube alongside other tools like Snyk or Checkmarx for a comprehensive security strategy.
Conclusion
SonarQube is a cornerstone tool in a robust DevSecOps strategy, enabling teams to maintain high code quality and security standards throughout the SDLC. By integrating it early and often, organizations can shift security left, reduce technical debt, and build resilient software systems.
As the demand for secure, high-quality applications continues to grow, leveraging tools like SonarQube ensures your DevSecOps initiatives remain proactive and effective. Start exploring SonarQube today and take a significant step toward embedding security into every line of code.